What is Network Service Orchestration (NSO)?
Network Service Orchestration or NSO, commonly refers to a software solution that helps network operators configure and automate multiple network elements as per a given service definition. Some examples of a network service include configuring L2 and L3 VPNs, On-boarding remote branch office equipment using zero touch provisioning, configuring Security and QoS policies for 3-Tier applications in Data Center, Configuring Bandwidth control and Application routing policies in a remote branch etc.
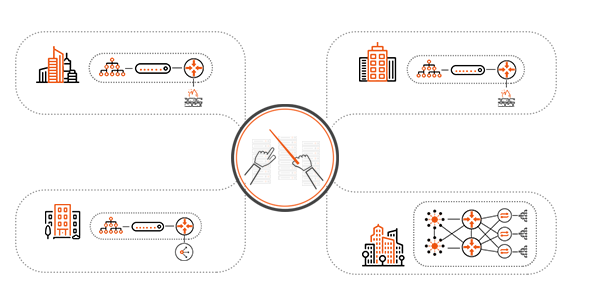
A network service typically spans multiple network elements such as routers, firewalls, load-balancers, VPN gateways, WAN optimizers, Web Security Services. These elements can be physical or virtual appliances and often sourced from different vendors (E.g. Arista, Brocade, Cisco, Checkpoint, Citrix, F5, Fortinet, Juniper, Huawei, Riverbed, Palo Alto Networks, VMware etc). The network elements may reside in an enterprise Data Center (also known as Private Cloud), a Remote Branch office, a Service Provider backbone network or in public cloud (such as AWS VPC).
Why Network Service Orchestration?
Traditional Network Management software is not able to keep up with the demands on the network operators. Every year, the underlying hardware keeps evolving (e.g. Fabric path, SDN controllers), the number of networking vendors increase and the communication methods (E.g. CLI, API, SNMP, NETCONF) keep changing. In many companies, the developer who wrote the expect or TCL scripts left the company and every simple change becomes a new project. Ultimately, network operators are resorting to spreadsheets to maintain VLAN numbers, Router credentials etc.
A Network Service Orchestrator uses the concept of abstraction to simplify the task of configuring multiple network elements. For example, let’s say the operator has to create a VLAN for a specific application. In the traditional approach, the operator has to login to each and every router and configure using CLI or GUI. On the other hand, a Network Service Orchestrator automatically discovers the network topology and all the dependancies for creating a VLAN. It auto generates the CLI or API calls for each vendor device and executes an atomic transaction across all devices.
To quote Ivan Pepelnjak, “Network Automation = Squeezing Grapes” and “Network Orchestration = Making wine”.
What are the minimum requirements for a Network Service Orchestration?
- Brownfield Discovery of Services and Devices
- Atomic Transactions across multiple network elements with auto roll back in case of failure in provisioning a single device
- Multi-vendor Support
- Integration with Northbound Systems (OSS/BSS, Ticketing systems, Workflow systems, Self-service portals)
- Integration with 3rd party software (IPAM, DNS, DHCP, Syslog Servers, Netflow collectors, Certificate Managers,
VNF Managers, Service Assurance and Analytics software etc) - Service Chaining and Service De-Provisioning including shutting down virtual appliances and removing ACLs
- IPAM and VLAN Management or integration with external IPAM systems
- Role Based Access Control at granular user, device and policy levels
- Extensibility to customize device models and service models to match business requirements
- Config Reconciliation to ensure policy is consistent with underlying infrastructure
- Zero Touch Deployment
- Device Credential Management
- Service Audit and History
- Capacity Management
How to compare multiple network service orchestrator solutions?

- Number of Vendors Supported
- Support and Depth of Brownfield
- Discovery and Orchestration
- Support for Physical and Virtual Appliances
- Ease of Customization
- Proprietary or Open Standards
- Scalability
- Validated Service Models
- Ease of using the Development Toolkit
Why select a vendor-supplied orchestration over an open source platform?
Open Source platform allows quick trial and appears economical in the short term. However, success of any Open Source platform depends on the community support. Current Open Source orchestrators such as ONAP, AT&T’s ECOMP, Telefonica OpenMANO NFV have not garnered the critical mass necessary for widespread adoption. Config management tools such as Ansible, Puppet and Chef have large community, but they are ideally suited for run-book automation for simple and repetitive tasks. There are also Open Source SDN controllers such as Open Contrail, Open DayLight with limited functionality in the Data Center.
Many organizations start with the Open Source approach and once they crystallize their requirements, they evaluate vendors against those requirements. The vendors have incentives to adopt latest technologies to offer a scalable and stable platform for their competitive differentiation. However, vendors cater to the majority of users. Hence, if you have a rare mix of network devices or if your service requirements are unique, an out of the box vendor solution will not work.
Anuta NCX is a vendor supplied orchestrator with extensible device and service models using industry standard IETF YANG models. Customers and partners can easily extend the models to customize the deployment as per their business requirements. Anuta Networks collaborates with technology partners to ensure on-going support for various vendor devices. As of August 2017, the NCX platform supports L2-L7 network appliances from 35 different vendors.
For the latest list, see Supported Devices.
What are the popular applications of Network Service Orchestration?
Network Service Orchestration is independent of the network topology and configuration. However, following scenarios are proven to benefit from NSO.
- Configuring L2 VPN and L3 VPN in multi-tenant environments
- On-boarding 3-Tier applications in a Data Center environment
- Zero Touch Provisioning of Remote Branch office equipment
- Configuring Identity, Access, QOS and segmentation policies in Campus environment
- Interconnecting Service Provider Cloud with 3rd party Public Clouds
- Provisioning Hybrid Cloud for Enterprise Applications
- Security Policy Automation across Multi-Vendor Firewalls
- Load Balancer as a Service
Comparison with other Networking Concepts and Tools
Config Management Tools – Chef, Puppet and Ansible
Chef, Puppet and Ansible are ideally suited for Run-book automation for simple and repetitive tasks. Many enterprises have successfully deployed one of these 3 tools for server automation. They typically bought an enterprise license that covers unlimited nodes. So, at the surface, it makes economic sense to use the same tools for networking.
However, these config management tools are still in their infancy with limited networking vendor support.
For a comprehensive Network Service Orchestration, a YANG model-driven platform approach is needed. For more on this topic, see Network Automation with Chef, Puppet and Ansible.
SDN and SD-WAN Controllers
SDN controllers introduce programmability, self-service and agility to a portion of the network infrastructure. Although some network elements are directly managed by an SDN controller, many are not. With a typical network service spanning many layers up and across the network stack including Data Center Access, DC Core, Edge, Campus, Branch/CPE, WAN etc. SDN controllers typically don’t have visibility across the entire stack.
SD-WAN solutions automate the CPE functionality but don’t cover the rest of the network that extends into a large campus/LAN involving routing, security, switching, wireless which requires configuration of QOS, segmentation, port security and identity based access policies. Take out the orchestrator, and manual configurations are required for multiple network elements including SDN controllers, OpenStack, VNFs, PNFs, servers and storage.
A Network Service Orchestrator complements the SDN controllers and helps deliver complete network service delivery across all network domains for your multi-vendor infrastructure.
For more on this topic, see Super Charge Your SDN Controller with the best Network Service Orchestrator.
Network Function Virtualization (NFV)
Service Providers are relying on Network Functions Virtualization (NFV) , an ETSI industry specification, to achieve on-demand delivery of network services by avoiding long hardware deployment cycles. ETSI NFV supports dynamic work loads by scaling out virtual network functions (VNF) using industry standard high volume servers, switches and storage infrastructure. Further, Network Functions Virtualization (NFV) enables the IT administrator to quickly identify capacity bottlenecks and migrate tenant services for effective resource utilization. However, support for VNF introduces new challenges such as placement, management and troubleshooting in a multi-vendor environment.
Anuta Networks NCX acts as the NFV Orchestrator and VNF Manager for leading L2-L7 virtual network functions from multiple vendor products such as Cisco CSR1000V, Cisco Nexus 1000V, Cisco XRV, VMware DVS, Citrix NetScaler VPX, F5 BIG-IP, Juniper vSRX, Juniper Firefly, Vyatta vRouter & Firewall and Riverbed Steelhead WAN Optimization. NCX delivers the complete NFV MANO functionality and offers life cycle management including VNF instantiation, placement, image management, service definitions, provisioning, commissioning and decommissioning.
For more on this topic, see NFV Management and Orchestration.
Intent Based Network Services (IBNS)
If Intent Based Networking represents Self-Driving Autonomous cars, Network Service Orchestration represents advanced driver assistance systems such as adaptive cruise control, Collision avoidance, lane change assistance features etc.
Hence, Network Service Orchestration is the prerequisite to deploying Intent Based Network Services.
Network Orchestration combined with telemetry data and feedback loops enables Intent Based Network Services.
How Network Service Orchestration improves Network Security?
While Network Service Orchestration doesn’t actively block security threats, it certainly improves the overall security posture of the entire network.
For instance, Network Service Orchestration:
- Avoids human errors related to configuration
- Ensures proper roll back of configurations and avoids stray configurations such as ACLs
- Enforces consistent policy across multiple vendor devices
- Captures audit history
- Maintains configuration backup
- Checks compliance and reconciles policy to eliminate config drift
- Enforces Role Based Access Control at granular device, user and policy levels
- Automates multi-vendor firewall policy management.
What role does Network Service Orchestration play in Service Assurance?
Network Orchestrator provides a single pane of glass for the entire service regardless of the infrastructure differences. For any given tenant, admin can view the service status, provisioned operations, current and historic SLA metrics as well as any alarms related to service health. This information is available through REST API for integration with OSS/BSS for billing purposes.
As part of the YANG service model definition, network architect can define SLA parameters (e.g. which interfaces and metrics to monitor). The YANG model also includes remediation steps when the SLA parameters are not met.
During service provisioning, Network Orchestrator validates the service model against the existing infrastructure and ensures capacity prior to provisioning the network elements. The Network Orchestrator generates commands and APIs for multi-vendor infrastructure as per the recommended best practices. Further, these commands are sent in an atomic fashion, so if any one device fails to provision, Orchestrator will roll back the configs from rest of the devices.
After service is up and running, admin can schedule periodic reconciliation tasks. Network Orchestrator uses its service model definition to discover the existing configs and makes sure the policy is consistent with underlying infrastructure.
Network Orchestrator constantly collects the SLA metrics and if any parameters are violated, it executes the remediation steps to automate corrective actions as per the YANG model.
For more on this topic, see Automate Network Compliance and Service Assurance for Multi-Vendor Network Infrastructure.